Introduction
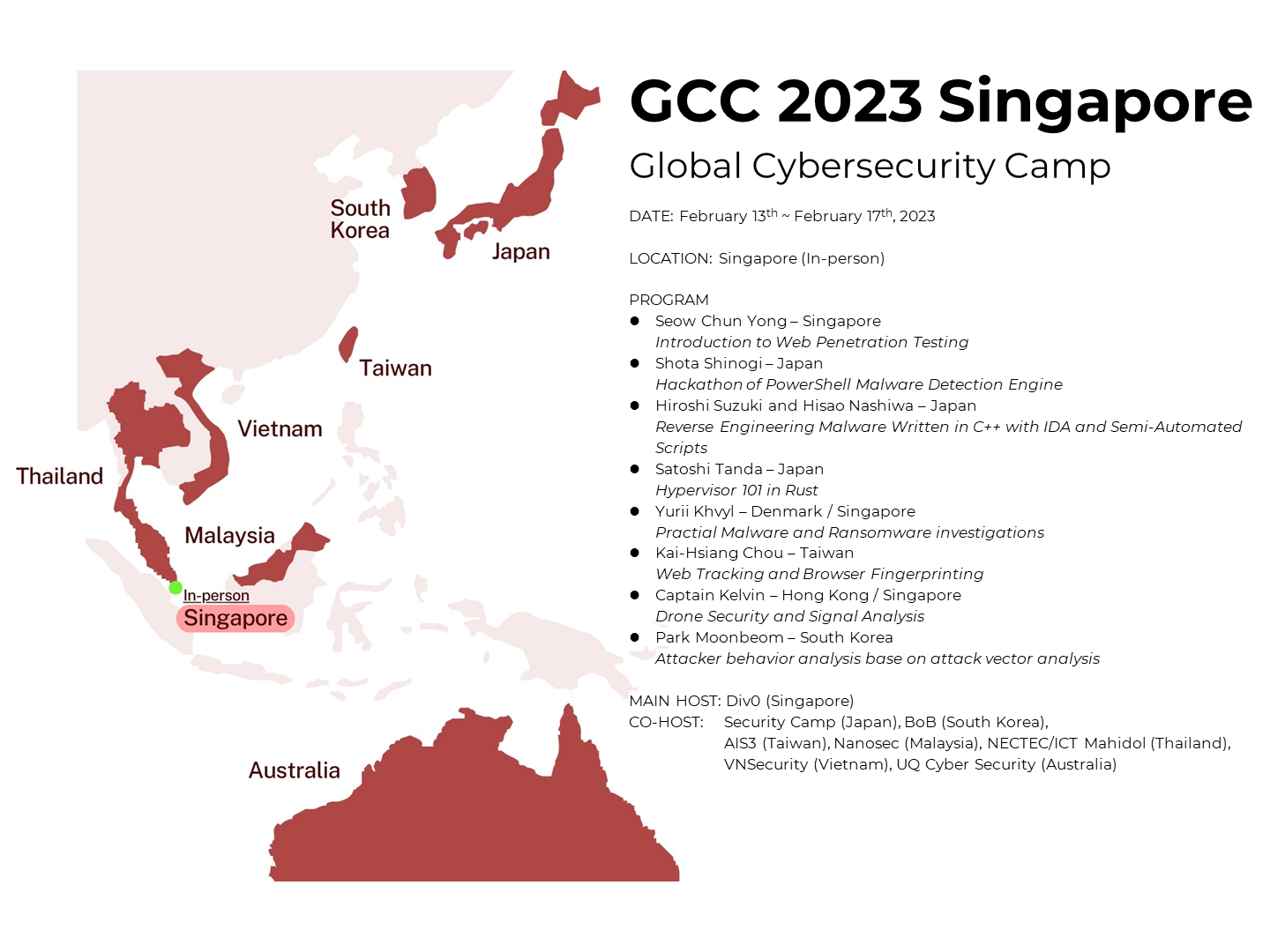
- Location: Singapore
- Days: 13th February ~ 17th February, 2023
- Eight countries are participating (maximum 48 students)
Mission of the GCC
Strengthen the security community across Asia and nurture future global leaders.
Annually, the best 48 students (maximum) from member countries gather in one of the participating countries for a week to exchange experience, forge a life-long friendship, and learn from the best cybersecurity professionals.
Non-commercial education programs and communities organize the program supported by industry leaders who care about the safe digitalization of the world.
Timetable of GCC 2023 Singapore

